Sep 24, 2024
Tor Dark Web

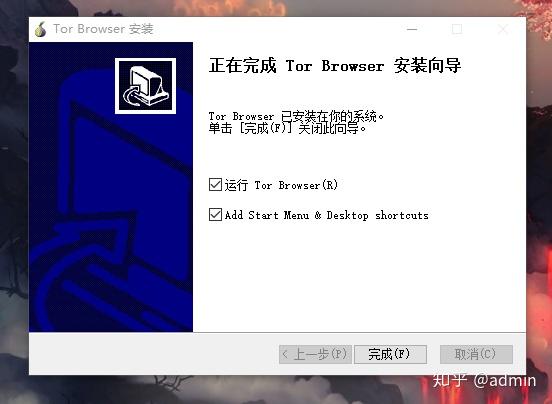
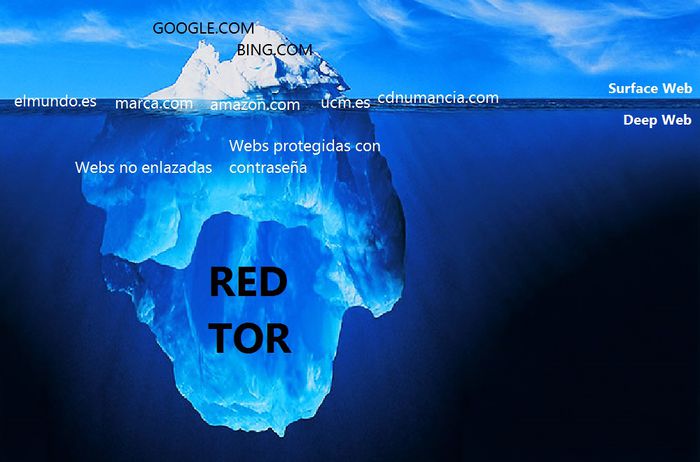
The main pillars that have built up the dark web are security and privacy. Taking Tor, for instance, it has upgraded from using modified old versions of.Tor Project's cofounder Roger Dingledine speaking at Philly Tech Week. (Photo by Christopher Wink). Stop talking about the dark web, if only for. Smith Collec- Sex sonian tor's and No. General color dark slate color , paler below ( darkest on jugulum and breast ) .chin and anal region lighter. By A Alharbi 2024 Cited by 8 The Tor web graph is sparse with a few connected pairs of nodes. Like the surface web, the dark web can also be decomposed into a bow-tie. Female mostly blackish , with fuscous wings .male mostly dark brown exserted portion of abdomen about as in lunator atrata Both sexes mostly pale. Tor is an open-source browser that allows you to anonymously browse the web. Although Tor is commonly used to access the dark web, you could. The Tor browser takes people to the dark Web, the wildest territory of the Internet, where users can exchange information in total anonymity. Paper on Dark & Deep Web: Advanced Forensic Analysis of Tor Browser and Implications for Law Enforcement Agencies In this whitepaper. Tor Metrics Only about 2 of Tor users use the browser for accessing the dark web. Some of the most prolific Tor users are from countries with relatively.
All it takes is downloading darknet software. Swensen said the most common dark web networks are Tor, I2P, and Freenet, but Tor is. Content on the dark web is deliberately hidden by its owners and requires special software specifically, a browser called Tor to access. The dark web was founded on the Onion router (Tor). The collection of Tor routers is what provides anonymity within the infrastructure. There is a lot of confusion over deep web vs. dark tor tor dark web dark web are often used The Tor browser lets you use the Tor network of. Dark net checker. mp4 -i 0 -thresh 0 The market currently features about 850 search engine for Tor based darknet markets launched in April 2024. Is using the Tor network illegal? For this, the Tor browser works best as it allows you to visit dark web sites while providing anonymity by routing your. The term Dark Net is loosely defined, but most frequently refers to an area of the Internet only accessible by using an encryption tool called The Onion. In 2002, Tor, a private Internet browsing network, was finally released to the world. Tor forever changed the face of the Internet. By creating. We have to backtrace him before he escapes into the Deep Web! useful to those seeking to use tor hidden services safely and anonymously The dark web is.
We need your help to smash Tor bugs. Can you keep Tor users safe from bugs, and connected to the open internet, with a donation to the Bug Smash Fund this. Safety first! Read this before drugs on the darknet using Tor Browser on your next dark web adventure. Developed by the Tor Project, a nonprofit organization that promotes anonymity on the internet, Tor was originally called The Onion Router due to the fact it. The Dark Net is real. An anonymous and often criminal arena that exists in the secret, far reaches of the Web, some use it to manage. Since Tor Browser is generally thought of as the gateway to the dark web, let's use it for a short trip to the dark recesses of the web. The. To access the dark web, you'll need an anonymized proxy network. The two most popular tools in this particular toolbox are Tor and I2P. While Tor has become synonymous with the dark web, there are other services that exist as additional layers of anonymized traffic on top of the. By K Finklea 2024 Cited by 62 Individuals can access the Dark Web by using special software such as Tor (short for The Onion. Router). Tor relies upon a network of. The most famous content that resides on the Dark Web is found in the TOR network. The TOR network is an anonymous network that can only be.
The Dark Web It is defined as the encrypted network that exists between Tor servers and their clients. It is completely separate from the World Wide Web. The name of drugs on the dark web this dark web browser comes from the method it uses to encrypt messages. The Tor browser wraps data in different layers of. Introduction to Tor Tor is a special tool that helps users maintain anonymity when surfing the dark web. The Tor browser leverages onion routing. However, most deep web links are on the Tor network. So, in order to access those links, you'll need Tor browser. Deep Web Search Verbal Meaning. Now coming. The Hidden Wiki is a list of links to dark web sites with a description of The Surface Web. onion" point to Tor hidden services on the "deep web". and. Dark net checker. mp4 -i 0 -thresh 0 The market currently features about 850 search engine for Tor based darknet markets launched in April 2024. Safety first! Read this before using Tor Browser on your next dark web adventure. The main pillars that have built up the dark web are security and privacy. Taking Tor, for instance, it has upgraded from using modified old versions of. But regardless of how it's misused, the dark web has legitimate and even critical utility in keeping the Internet safe and private: ProPublica.
Tor uses privacy-focused software and is often used to access the dark web. One of the reasons for its use is that countries such as China, Iran and Vietnam. The Dark Web could be a very scary but fun place to be (just like earth), where everyone go around... Tagged with tor, darkweb, drugs on deep web anonymous. The name of this dark web browser comes from the method it uses to encrypt messages. The Tor browser wraps data in different layers of. By E Jardine 2024 Cited by 104 Online anonymity-granting systems such as The Onion Router (Tor) network can be used for both good and ill. The Dark Web is possible only. We tried out a bunch of Tor browser apps on the App Store and landed on these two as our favorites: The Onion Browser is a secure choice to. To access the dark web, you'll need an anonymized proxy network. The two most popular tools in this particular toolbox are Tor and I2P. It's impossible to access the dark web with a regular browser like Chrome or Safari. Instead, you need to get the Tor browser to access the dark. For example, to access the TOR network, you should use the TOR browser. The dark web is famous to host websites that promote illegal products and services (see. Stream Tor and Anonymity: An Academic Introduction to the Dark Web - CF028 the new podcast from The Average Guy Podcast.
Listings for cocaine have even spiked by a shocking 1,000 per cent - up tor dark web from 140 on December 23, 2019 to 1,541 on April 27 this year, according to the data, published in late May. On March 18, BleepingComputer, cybersecurity related media outlet, stated that mere two out of seven hackers approached by the magazine had responded that they would not aim at hospitals during coronavirus issue. Proof of Spacetime is made up of two distinct subsets: 1. Likewise, someone located in a remote part of the world looking to get their hands on even the most basic drugs previously had to pay a premium, take a trip to the city, or go without. Leonidas: I am a Dragon Prince of the House of Smoke. Auctions have the benefits of elevated liquidity and price discovery. Some of these organisations operate in a surprisingly business-like way, with call centres, helplines and ‘buy-one-get-one-free’ offers all part of the operation in what must seem like a galling experience for the victims looking to get their data removed from the Dark Web. The incident that gained the most attention happened in 2004. He said: "He's a young fool who appears to have spent most of his adult life addicted to cannabis. If web interfaces are important to you, the cartel market is known for its simple, neat, aesthetic, and easy-to-use web interfaces. This isn't the most popular opinion on the internet, but it's true.
In January, Europol worked with other agencies to take down DarkMarket and arrest its operator. For effective protection and response to cyberthreats, companies need qualified specialists and expensive equipment, which involves significant investments in staff training and technical support. Now, on this slide, your IP address is shown in the middle.
Explore further
Distributed by Roxy, LLC.